One of the things that we see when responding to security events is that each event is unique, which makes it interesting. There are silos, for example within DLP we have egress unencrypted email attachment as one silo, then have egress unencrypted one’s own personal information, egress encrypted potentially secret, egress unencrypted secret, and maybe one or two others. Below is a chart for the Private Information Domain when performing data leakage prevention measures and analyzing data coming in but only one domain. There are others related to egress of company secret IP and other types of information that should be encrypted via email.
Private Information Leakage Scenarios
| Event Silo | Scenario 1 | Scenario 2 | Scenario 3 | |
| egress unencrypted email attachment | Personal contact list to/from work email | Forms to customer unencrypted | Forms or work papers to personal email | |
| egress unencrypted one’s own personal information | HR communications | Social welfare communications | Finding new job |
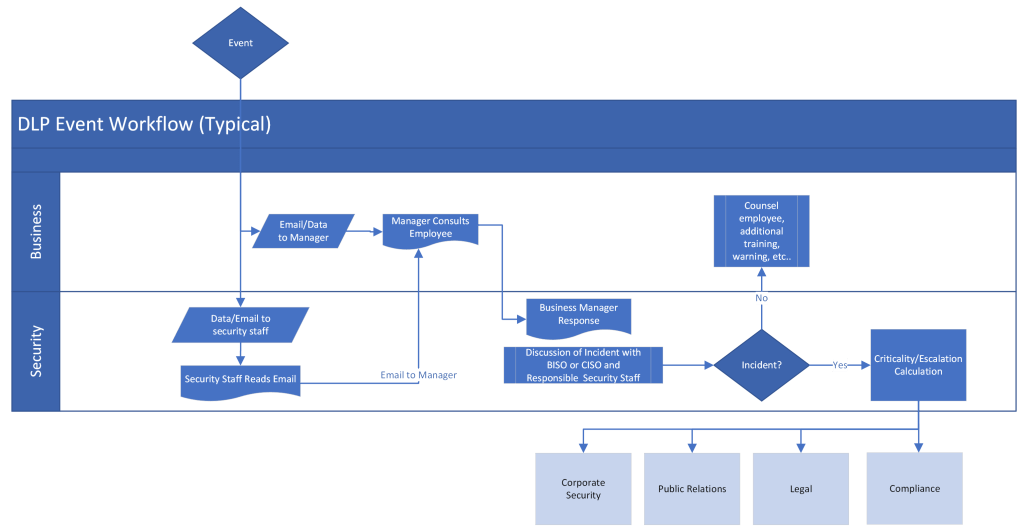
Scenario three above are both higher risk, scenario one and two for egress unencrypted email attachment is medium risk, and the two below that are low risk. Identifying these differences in risk changes the event handling, but these scenarios are very general and an actual scenario requires human intervention for event analysis. A typical DLP event handled up to the incident process shown below indicates where humans are interacting. In the earlier stages of this process, a bit of time is taken in email and telephone confirmations, which could actually be better implemented in the form of an email-driven workflow. This immediately helps to fulfill the timely requirement as each email is queued for review, and we can rest assured that each event is initially handled in a uniform manner.
Accurate Analysis
Making sure that the handling is uniform and timely in the early stages is easily resolved with an email-driven workflow, but to enhance monitoring even during the event handling and review process will provide a bit more confidence if the event you are processing is, in fact, an incident to be reported. There are a variety of ways to do this through key logging, security camera analysis, desktop mirroring, but one of the best ways in higher risk environments is to implement an activity recording system.
As mentioned earlier, while we can silo events into major groups, almost all events are unique, so it’s difficult to determine if an event was evaluated accurately. An activity recording system would facilitate the accuracy requirement by being activated according to DLP rules and policies. One scenario is where an employee updates their resume on a company computer then sends that document to their personal email. The reviewing manager may see this as a risk due to job sensitivity, and could start activity monitoring. The additional monitoring information could further determine the handling. Would just counselling the employee about using company time and resources to update their resume suffice? Or, open an incident and investigation as we see other confidential or above information leave on egress channels? Either way, an activity recorder will provide the most accurate path for event handling; especially, for higher risk environments.
Accurately responding and handling implies policy compliant, but standardized handling does not imply proper nor accurate event handling – when it comes to any event alert system. Uniqueness means that human intervention for review is required, which can be supported by workflow tools, then as each escalation and criticality is assessed, the process can be supported through activity recording. This particularly applies to DLP, where all alerts may be an event or incident in process, versus a detective alert that shows an event may have already happened.
Timely Handling – Automate the Workflow
If you can standardize the handling and ensure timely responses, you’re half way there and providing more time for deeper analysis where necessary. The diagram below presents an example workflow solution, which streamlines communications by pushing the reviews through email from the DLP software solution (yellow gear – DLP/CASB Solutions) to a workflow manager that handles logic and mail forward tasks. This pushes with time to ensure that not only reporting and next level see events but need to handle the event analysis task to push the workflow forward. DashMagiq currently offers solutions for most major DLP solutions on the market (Mcafee, Symantec, and Digital Guardian).
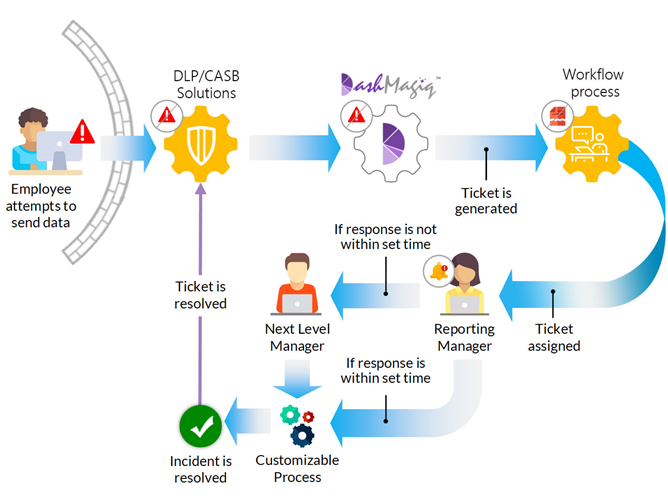
DashMagiq logic engine stores all the forwarding and decision rules for handling. As events are past to the reporting manager, his/her decision is then reflected off the customizable logic engine to determine next level of handling. The diagram above uses simple time triggers for thresholds, but others based on information sensitivity can also be readily implemented.
Consistent Handling
This is an area where humans can fail miserably, but are often saved by procedures, policies, and manuals, but in this case supported by a workflow. Given a workflow and a variety of event analysis scenarios, the seasoned manager becomes consistent in handling, but without an automated workflow that learning curve becomes much steeper. Consistently handling events into incidents or any other treatment is very important, since you do not want to be in a situation where employees see that they were treated different for basically the same email infraction. As mentioned before, this is where strong policy, clear procedures, and a documented (and preferably automated) workflow are essential.

